Sorry, nothing in cart.
Google Docs Forms Abused by Phishers to Harvest Microsoft Credentials
- By michael@cvcteam.com
- |
Security researchers detected several phishing campaigns that leveraged a Google Docs Form to target users’ Microsoft credentials.
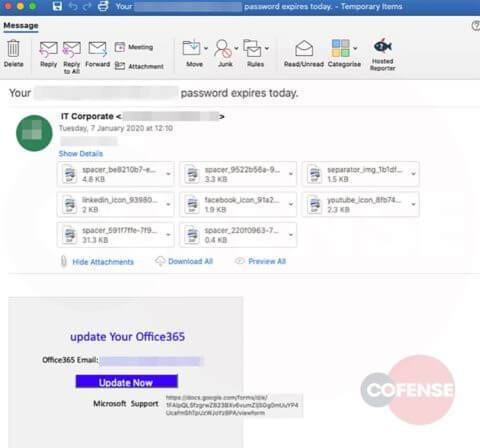
Cofense observed that the phishing emails originated from a compromised email account with privileged access to financial services provider CIM Finance. By using CIM Finance’s website to host their phishing emails, the malicious actors ensured that their messages could bypass popular email security checks including DKIM and SPF.
The emails themselves masqueraded as notifications from the IT team informing recipients that they needed to “update their Office 365” if they wanted to prevent the suspension of their accounts. By creating this sense of urgency, nefarious individuals attempted to pressure recipients into clicking on the “Update Now” button.
It’s at that point when the Google Docs Form came into play. As explained by Cofense in its research:
This threat actor set up a staged Microsoft form hosted on Google that provides the authentic SSL certificate to entice end recipients to believe they are being linked to a Microsoft page associated with their company. However, they are instead linked to an external website hosted by Google….
With this setup, phishers created a fake Microsoft Office 365 login page. This page distinguished itself from Microsoft’s legitimate login page by capitalizing close to half of the words and sometimes replacing letters with asterisks. The phishing page also displayed users’ credentials in plaintext as they typed in this detail into the form’s input fields.
Upon submitting their credentials, the campaign sent this information off to the attackers via Google.
This attack highlights the need for organizations to strengthen their email security. One of the ways they can do this is by raising their workforce’s awareness of some of the most popular phishing attacks in circulation today. Towards this end, organizations can use this resource as the beginning of an ongoing security awareness training effort.
Leave a Reply